The quarantine is tough, but for those who enjoy spending time at home, it isn’t that bad. And what better way to spend countless hours at home than playing immersive video games? Game developers and publishers are reporting an increase in sales, which is excellent. Even though some game releases have been postponed due to everyone working from home.
There’s one alarming trend in the game industry that, sadly, increased during the quarantine. That’s hacking attacks directed against gamers. According to cybersecurity news at portswigger, there’s an increase in DDoS attacks, SQL injections, and credential stuffing. The last one – credential stuffing attack – is easily executable and is gaining in popularity due to decent financial gains. Luckily, it’s very easy to defend against, so we’d like to explain to you what credential attack is, and how you can protect your gaming accounts.
What is a Credential Stuffing Attack?
First Credential stuffing attacks appeared in 2014 and over the last couple of years rapidly increased in popularity. In fact, they became so common that even the FBI in the United States released a Private Industry Notification, warning that the US financial sector became targeted by cybercriminals. And numerous password privacy cybersecurity companies are alerted to take better care of your online accounts.
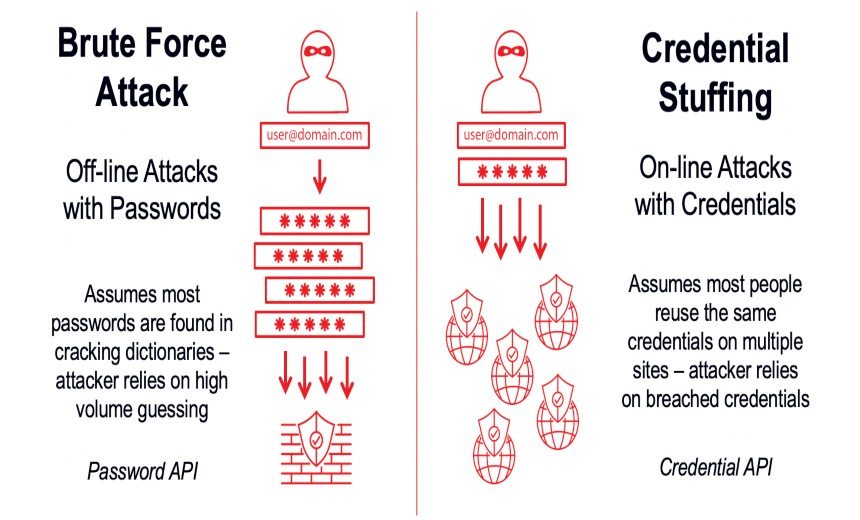
A Credential stuffing attack is a type of cyber attack that is surprisingly simple to execute. Typically, the attack involves four easy steps and requires minimal effort on the part of the attacker. The first step is for a significant number of username-password combinations to be leaked online from an insecure service, which unfortunately happens more often than it should. This leaked information is often sold on the Black markets of the web. Once a cybercriminal has obtained a dataset of leaked username-password combinations, which are known as combolists, they can use them in a Credential stuffing attack. To protect yourself against this type of attack, you may want to consider using a service from Fully-Verified or another reputable provider, which can help you secure your login credentials and prevent unauthorized access to your accounts.
Next step is to obtain an automation software, which can be purchased for several dollars. With the help of this software, the hacker then targets another service with leaked credentials, in hopes that the same username and password were reused. And if this turns out to be the case, the account is stolen and most often sold on the same black markets.
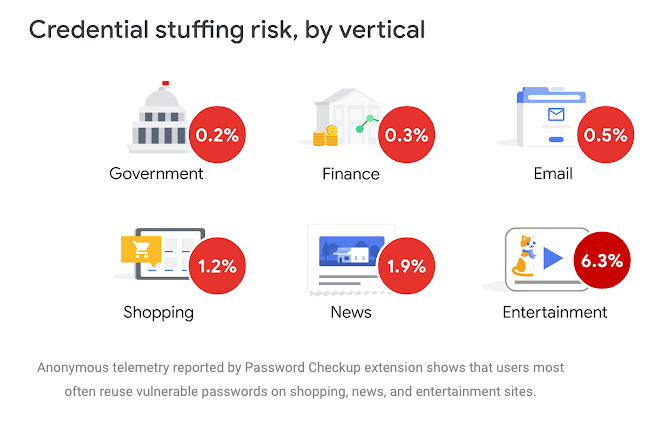 One of the more recent cases of successful credential stuffing attacks is the Disney+ case, which happened right after the launch. Cybercriminals had a vast collection of combolists, and right after the release of this new popular streaming service, targeted it with acquired credentials. The success rate proved to be high, and soon Disney+ accounts were sold for half the price on online Black Markets.
One of the more recent cases of successful credential stuffing attacks is the Disney+ case, which happened right after the launch. Cybercriminals had a vast collection of combolists, and right after the release of this new popular streaming service, targeted it with acquired credentials. The success rate proved to be high, and soon Disney+ accounts were sold for half the price on online Black Markets.
The crucial thing to notice is that this attack can only succeed if the same username-password was used. Sadly, password management is still a problem, and such easy-to-guess passwords as “qwerty” or “password” or “123456” are still used. And that is precisely why this attack became so popular. It’s very easy to execute and requires little “hacking” in the traditional sense of the word. And lousy password management practices ensure this attack is profitable to a cybercriminal. Regularly change passwords and use a strong password checker to keep them secure.
Luckily, there are easy ways to protect yourself against these kinds of attacks, so go straight ahead to the next paragraph, where you can take the first steps to secure yourself online.
How to Protect Yourself Against Credential Stuffing Attacks?
 The first step, obviously, is not to use the same username-password for different services. However, it’s harder to do than it sounds, because we use so many other services these days, that there would be a need to remember hundreds of passwords. But password managers are there to help! Password managers are cybersecurity software that was designed to store large amounts of long and complex passwords. Remembering a 60 symbol password with upper and lower case letters, and numbers can be challenging for the best of us. And remembering a lot of passwords like this is nearly impossible.
The first step, obviously, is not to use the same username-password for different services. However, it’s harder to do than it sounds, because we use so many other services these days, that there would be a need to remember hundreds of passwords. But password managers are there to help! Password managers are cybersecurity software that was designed to store large amounts of long and complex passwords. Remembering a 60 symbol password with upper and lower case letters, and numbers can be challenging for the best of us. And remembering a lot of passwords like this is nearly impossible.
Password managers quickly rose to popularity. Not only do they boost your cybersecurity significantly, but they also provide a more comfortable browsing experience due to autofill function. You can actually save time when browsing with a password manager because you don’t have to type passwords anymore and import them straight from the manager with one click. The best password manager for Mac is very useful to secure your various accounts.
Another service we’d advise using is a www.haveibeenpwnd.com website, that was created by a prominent cybersecurity expert Troy Hunt. On it, you can check your email address for leaks so that you know which one of your passwords have been exposed and can change it to a more secure one. Using a disposable email address from 10 Minute Mail to register on websites, blogs, and forums keep your real one hidden from hackers’ eyes, thereby improving email security. These steps do sound easy, but even small changes can be crucial and defend your account against a cybercriminal looking for an easy grab. And what could be worse than losing your steam account with all the games on it?
We hope this has been informative and will help some of you secure yourself online better!
This article contains sponsored links.


























































[…] type of crime is called credential stuffing. And online entertainment is one of the most common types of […]
[…] genre de crime est appelé «bourrage de justificatifs d’identité». Et divertissement en ligne est l’une des voies d’attaque les plus […]